Introduction
A new feature has just rolled out of preview into general availability and its a good one!
With the ever progressive move to Cloud-based VDI solutions there is often a question mark surrounding the security of these platforms.
I’ve had numerous conversations with customers and colleagues alike that have concerns about the security of remote based VDI environments.
I think however that platforms like Azure Virtual Desktop are a little more secure than people might think. Firstly, you can control access to the platform via Azure AD with Multi-Factor Authentication, the Reverse Connect connection model also allows for only outbound initiated connections to the session host via the broker.
You can then lock down access to things like Drive and Clipboard redirection via the RDP settings in the Portal (or Group Policy if you prefer) just like in an On-Premises environment.

The one thing you couldn’t do however, was stop users from taking screenshot of the actual RDP Client connection. That was until now, enter Screen Capture Protection.
Screen Capture Protection allows you to control whether users will able able to screen capture the in progress Remote Desktop Session. This is exclusive to the Desktop Client.
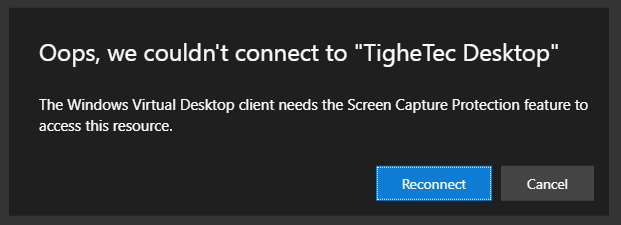
If configured you will no longer be able to login via the Web Client and will recieve this message.
This is a great feature and allows customer to know there data can only be accessed from within the actual remote session and no details can be shared from outside of this session.
This feature was originally in preview but as of this month (September 2021) is now in General Availability.
This blog will explain how you can confirm this feature and show the effects.
Instructions
Although this is now a General Availability feature it is not available to configure via the Azure Portal. So we will need to get our hands a little dirty with a quick registry change.
Firstly, we shall show that I am 100% able to screenshot my AVD client prior to configuring the Screen Capture Protection feature.
So now to fix this and ensure that I can’t take screenshots anymore.
You can make this configuration change directly via the Registry or using the Azure Virtual Desktop Group Policy module found here: https://aka.ms/avdgpo
Manual Registry Change
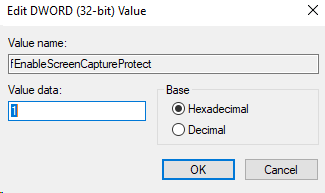
For the Screen Capture Protection to work we need to make a registry change on the Session Hosts. No obviously I would normal make this change on the golden image, or on mass via something like Microsoft EndPoint Manager.
In this instance however, I will make the change manually on my single Session Host.
First, I login to the offending Session Host. Then open Reg Edit
Add the following registry key
Under the HKLM\SOFTWARE\Policies\Microsoft\Windows NT\Terminal Services key.
Group Policy Change
Ensure you have the relevant Azure Virtual Desktop group policy administrative template installed on my DC/Central Store.
Once the Administrative template is installed. Open up Group Policy Management and create a blank GPO.
Next edit the new GPO and find the Computer Configuration > Polices > Administrative Templates > Windows Components > Remote Desktop Services > Remote Desktop Session Host > Azure Virtual Desktop node.
Configure the Enable screen capture protection and set it to Enabled.

Assign the GPO to the required OU.

Then either wait for the GPO to apply or run a handy GPUpdate /force on the test machine.
If your test user was logged in, then log out as the change won’t take effect until this is done.
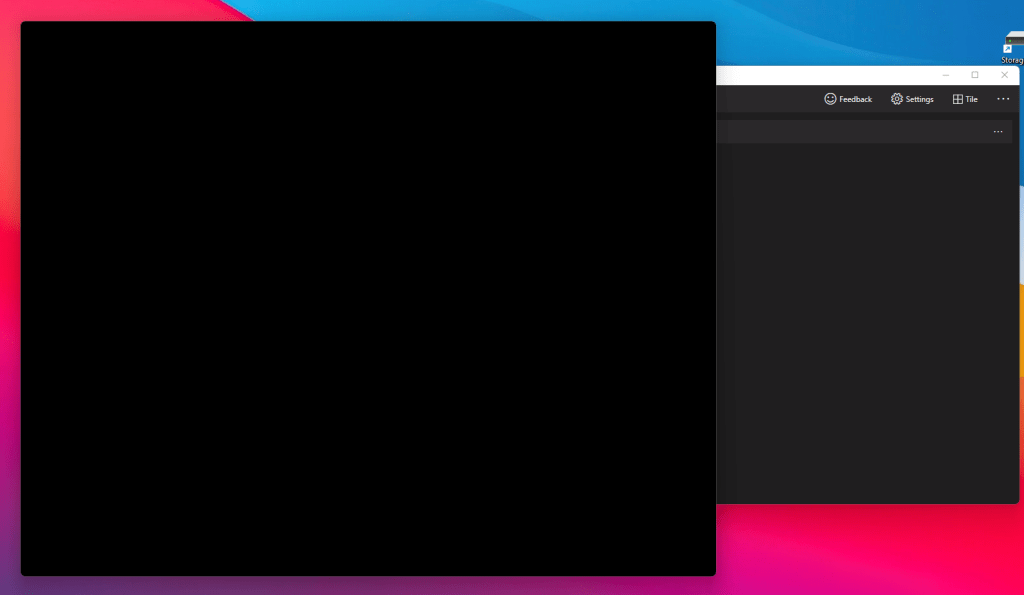
Now I can see that I am unable to take a screenshot of the Remote Desktop screen. Success!
Conclusion
So there you go, a quick and easy way to add an extra bit of security to your Azure Virtual Desktop environment.
Just be aware as mentioned that you will not be able to login via the Web Client if you enable this feature. As there is no way to control screenshots outside of the Desktop Client AVD disables the access.